by WorldTribune Staff, June 2, 2022
A recount of the May 24 primary in Georgia’s DeKalb County shows a difference of more than 2,800 votes between the machine count and the hand count.
The hand recount was conducted in the District 2 County Commission race after questions were raised over equipment “malfunctions.”
DeKalb Voter Registration and Elections Office Executive Director Keisha Smith issued a press release to distribute the recount tabulation which changed the results and the runoff participants.
The DeKalb Voter Registration and Elections Office originally reported that the June 21 runoff for District 2 County Commission was between Marshall Orson and Lauren Alexander, with Michelle Long Spears in third place and missing the runoff. After the hand recount, Spears’s vote total increased by 3,620. Orson’s total decreased by 1,298. Alexander’s total increased by 355. After the recount, Alexander and Spears will go head-to-head in the runoff.
“The press release does not explain the large discrepancy between the machine count on Election Night and the subsequent hand count. It also doesn’t explain the appearance of 2,810 more votes cast than were initially reported,” Decaturish reported on June 1.
“Had Spears not raised questions on Election Night, it’s unclear whether the result would be in doubt at all,” Dan Whisenhunt wrote for Decaturish. “Some precincts were reporting she received zero votes – including her own precinct. Spears took pictures of the precinct-level results and showed them to Decaturish on Monday during day two of the hand count. Her supporters, including commissioners Jeff Rader and Ted Terry, began publicly raising questions about what happened.”
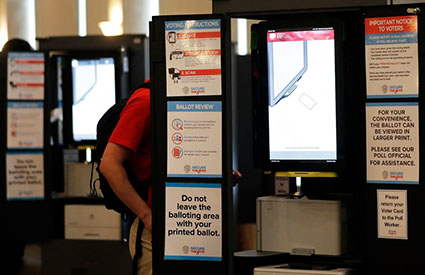
The U.S. Cybersecurity and Infrastructure Agency (CISA) reported last month that 16 states are using Dominion Voting Systems software which is vulnerable to hacking. Georgia is one of those states.
One of the most serious vulnerabilities could allow malicious code to be spread from the election management system to machines throughout a jurisdiction, University of Michigan computer scientist J. Alex Halderman said. The vulnerability could be exploited by someone with physical access or by someone who is able to remotely infect other systems that are connected to the internet if election workers then use USB sticks to bring data from an infected system into the election management system.
Several other particularly worrisome vulnerabilities could allow an attacker to forge cards used in the machines by technicians, giving the attacker access to a machine that would allow the software to be changed, Halderman said.
“Attackers could then mark ballots inconsistently with voters’ intent, alter recorded votes or even identify voters’ secret ballots,” Halderman said.
About . . . . Intelligence . . . . Membership
